Listen Here: Malware Can Be Transmitted Through Audio
Researchers have shown how computers can be hacked even without being connected to a network.
 Credit:
Credit:
Recommendations are independently chosen by Reviewed's editors. Purchases made through the links below may earn us and our publishing partners a commission.
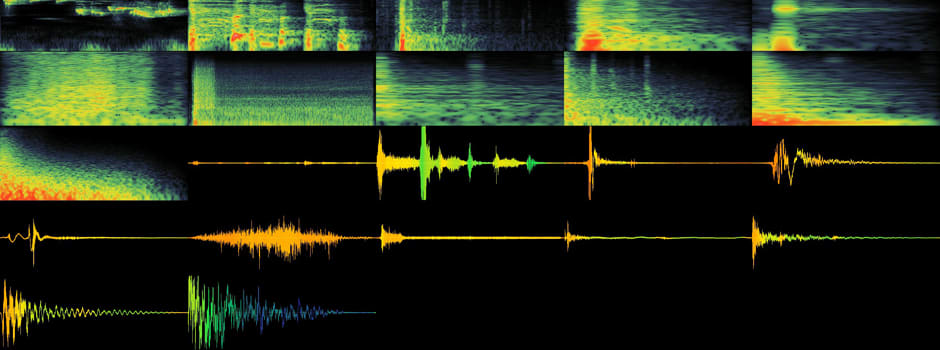
Simply disconnecting your laptop from the internet might not be a failsafe against hackers. Researchers at the Fraunhofer Institute for Communication in Germany recently demonstrated how a super-high-frequency audio signal—one imperceptible to human ears—can be used to transmit data to and from a personal computer.
The scientists developed an experimental malware program that was successfully transmitted to nearby laptops—all without being connected to a network, and with nothing but the sound processor, speakers, and microphones that come standard on most computers.
While these HF signals are only effective up to a range of about 65 feet, the researchers also demonstrated how "acoustical mesh networks" can be constructed in the same manner. This would allow hackers to extend an audio-based network across a large area using nothing but inaudible signals, rendering the activity virtually undetectable.
"It is shown that the concept of a covert acoustical mesh network renders many conventional security concepts useless, as acoustical communications are usually not considered," wrote the report’s authors, Michael Hanspach and Michael Goetz.
Of course, there are some countermeasures. Hanspach and Goetz recommend simply switching off the audio input and output of susceptible devices. One could also install filtering programs to block high-frequency signals, although such applications are not often built in to computers. The authors also proposed a software architecture that's specifically designed to inspect incoming and outgoing audio.
"The audio intrusion detection guard would forward audio input and output signals to their destination and simultaneously store them inside the guard’s internal state where they are subject to further analyses," the report states.
The thing about hacking is, if something is possible, someone is likely to exploit it. While this discovery may not be cause to immediately go out and purchase a high-security audio filter for your MacBook, it's indicative of the endless, unpredictable array of security threats facing an increasingly digital, connected world.
These concerns extend beyond personal computing. Experts fret about the vulnerability of new tech concepts like the smart home and the internet of things. As we hand off more and more of our responsibilities to smart machines—from locking our houses to driving our cars—we run the risk that they might be corrupted by malicious computer experts.
Via: Journal of Communications
[Hero image: Flickr Creative Commons, "Iwan Gabovitch"; Network image: Creative Commons, "OLPC"]

